
Phishing
Phishing is a type of social engineering attack in which an attacker, pretending to be a trusted entity, tricks a victim into opening a fraudulent email, SMS or website. The victim is then lured into clicking a malicious link or opening an attachment, which can lead to the installation of malware, the freezing of the system as part of a ransomware attack or the revealing of sensitive information.
Victims may suffer the following losses if they inadvertently provide sensitive information or open a malicious file attached to a phishing email:
- Victims’ user ID and passwords will be used to gain unauthorized access to their internet banking and steal money from their accounts.
- Victims’ credit card information will be used for making fraudulent transactions, causing debts for the unwitting victims
- Attackers can impersonate victims who are trusted company figures, such as owners, and send an email with instructions to issue a funds transfer to their own account.
- Leak of victims’ personal data such as salary and financial status.
- Attackers may encrypt victims’ files and demand ransom for victims to be able to access their files. (Ransomware).
How do scams work?
Theft of internet banking information
Victims receive a phishing email that pretends to act as their bank’s security division, requesting personal information and asking victims to enter an OTP (one-time password) obtained from their mobile phone. Then, attackers use that information to access the internet banking services and transfer victims’ funds to their own accounts.
Theft of credit card information
Customers of an online movie service receive a phishing message informing them that the service has been temporarily suspended. The victim is then asked to click on a link, which belongs to the attackers to update their personal information. Then, the attackers use that information to impersonate the victim online to perform fraudulent transactions.
Ransomware that hijacks computers
Attackers send an email to a victim telling them to install a program attached to the email, for security reasons. Once the ransomware has taken over the victim’s computer, it runs a code that encrypts the victim’s data, and the attackers then demand a ransom from the victim, promising - not always truthfully - to restore access to the data upon payment.
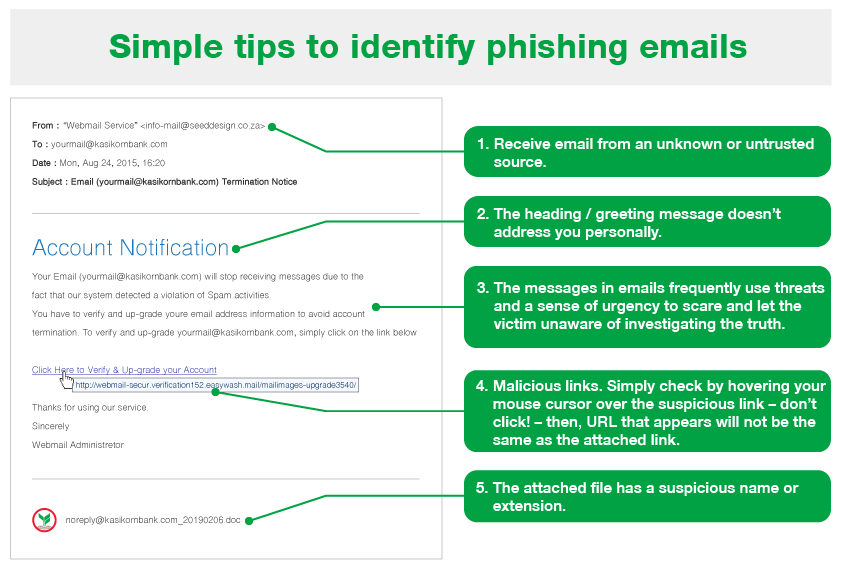
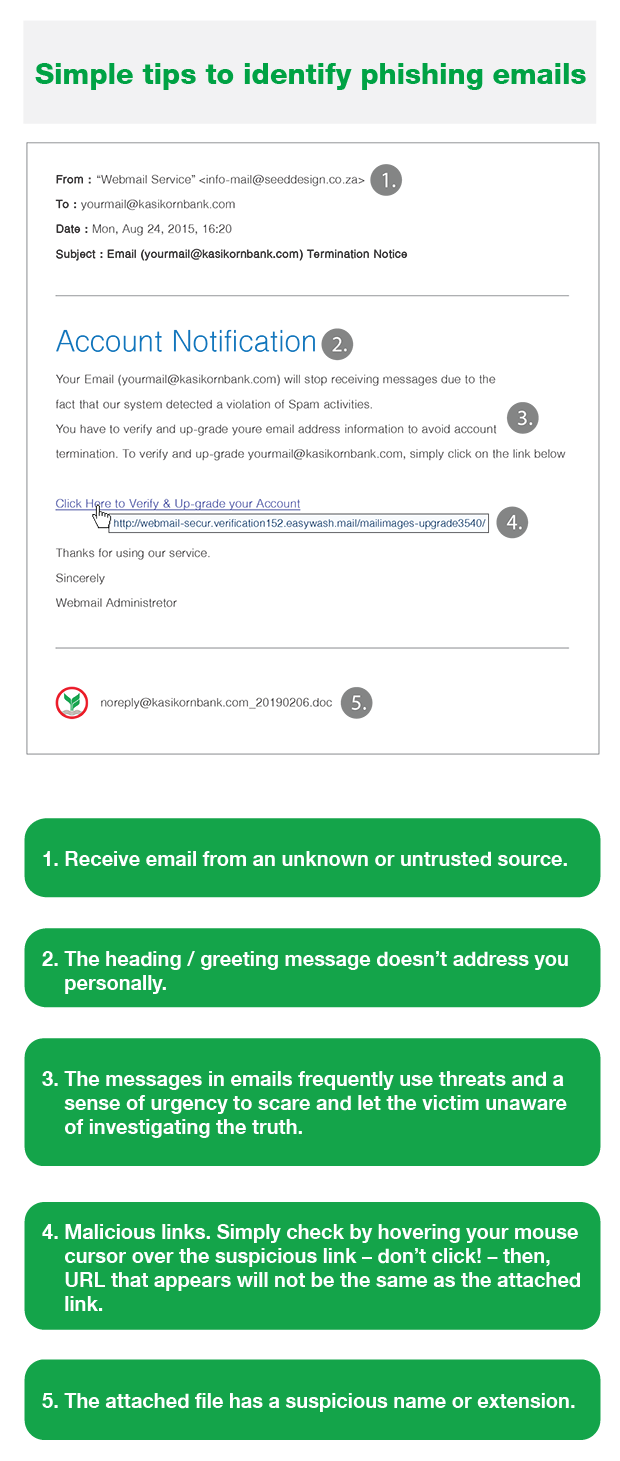
How to identify scams
The email/SMS sender does not raise suspicion at first, but on closer inspection is actually unknown to you.
The language in the email/SMS is informal, contains grammar mistakes, and seems awkward or unnatural upon reading, somewhat like the text resulting from machine translation.
The content is unusual, and may ask you to act immediately in order to prompt you into clicking the attached link or providing sensitive information.
Malicious links can be detected by moving the mouse cursor over them - don’t click! - then, a different URL or email address will appear, or it may look like a legitimate one which has been changed slightly or contains added characters.
Attached files may have a suspicious file name or file extension.
How to protect yourself from scams
Don’t panic when you receive a suspicious email or SMS. Look at it carefully to determine if it has the characteristics of a phishing email.
Need to know Aware that banks and other financial institutions have no policy to send an email with an attached link or file to request information from customers.
Don’t click on a link or open an attached file in a suspicious email / SMS.
Confirm the message with the sender or another trusted source of information, such as a bank’s call center.
Delete the email/SMS and do not forward it to others if you suspect that it is a phishing email/SMS.
What to do when falling victim to scams
-
In case of username and password already provided in response to a phishing

Change your password immediately.

Create a secure password, difficult to predict. Don’t use the same password for every account.

Turn on two-factor authentication.
-
In case of bank account or credit card or ATM card information already provided

Call to inform the bank to freeze your account or cancel your credit card (if possible).

Check your account movements regularly.

If any financial loss is detected, gather the evidence and report to the police and contact the bank to suspend the recipient’s account.
-
In case of opening a file or installing a program that contains malware

Install an antivirus program and scan your computer.

Change your password immediately after removing the malware.
KBank has no policy to send customers a link
or attachment file for filling in personal or account information.